I cannot honestly believe it’s already time for our user group meeting. It’s one week from now. It’s kind of crazy how fast time goes by. It’s also a lot more effort to put these together than you would expect.
So for that, I am grateful to all of the folks that help keep this going, all of the sponsors that help keep us eating, our perpetual sponsors that give us lots of great giveaways and benefits, all of the speakers that bring great content, and all of the people, like you, that come share your knowledge.
At our last user group meeting, we took an opportunity to use the space in the MTC side of the Microsoft office. What we discovered was the interaction was entirely different than the classroom spaces. It provided a better environment for interaction which is ultimately what we’ve always strived for -- networking, meeting your peers in the industry, and sharing knowledge. That’s the benefit of tying into a user community. You grow your access to knowledge exponentially.
Shavlik is our sponsor this quarter. Their product addresses the big hole of patch management where Windows patching ends -- third party. Here’s a little blurb:
Today, it's not Windows that represents the most vulnerabilities, but instead it's the applications that run on Windows that expose businesses to holes in computing security. The National Vulnerability Database reports that 86% of reported vulnerabilities come from third party applications. With Shavlik Patch for Microsoft System Center, administrators have the ability to automate the patching of third party applications within the System Center Configuration Manager console, providing confidence that third party application vulnerabilities are covered.
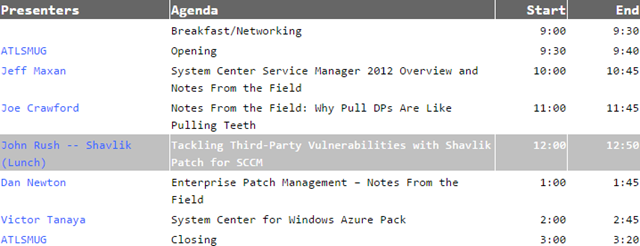
Here’s the rest of the schedule:
We have three seats left by last count. The drawback to using the MTC space is we lose some room so we’ll be running a tight ship trying to maximize all the seating available. If you haven’t registered yet, there’s still time! Get all the details here, including the registration link: http://www.atlsmug.org/events/atlanta-systems-management-user-group-100314
See you there!
Comments
Post a Comment